New breakthrough enables perfectly secure digital communications
A team led by University of Oxford researchers has achieved a breakthrough in secure communications by developing an algorithm that conceals sensitive information so effectively that it is impossible to detect that anything has been hidden.

This breakthrough in secure communications promises unprecedented levels of security and efficiency to its users, who may enjoy a much higher extent of plausible deniability than with previous steganographic methods. We will be working with all relevant communities of stakeholders, including humanitarian aid workers and investigative journalists, to unlock its potential in the real world.
Dr Christian Schroeder de Witt, Department of Engineering Science, University of Oxford.
Working in close collaboration with Carnegie Mellon University, the researchers developed a new method which they envisage may soon be used widely in digital human communications, including social media and private messaging. In particular, the ability to send perfectly secure information may empower vulnerable groups, such as dissidents, investigative journalists, and humanitarian aid workers.
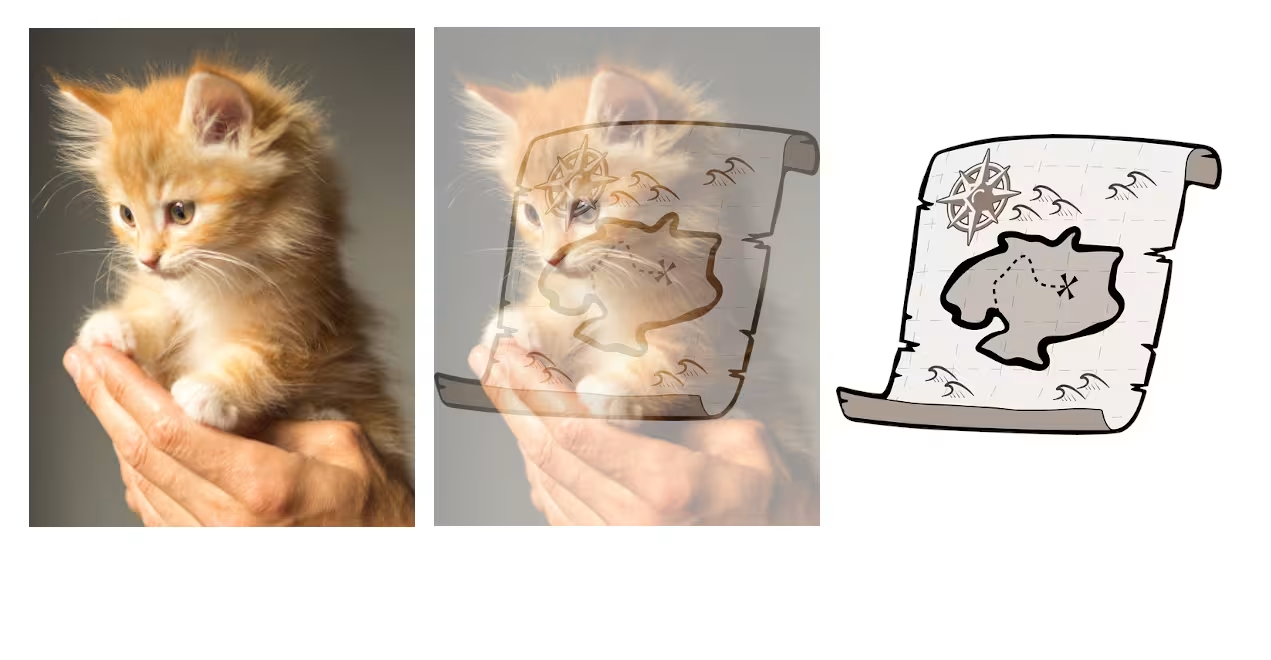
The algorithm applies to a setting called steganography: the practice of hiding sensitive information inside of innocuous content. Steganography differs from cryptography because the sensitive information is concealed in such a way that this obscures the fact that something has been hidden. An example could be hiding a Shakespeare poem inside an AI-generated image of a cat.
Despite having been studied for more than 25 years, existing steganography approaches generally have imperfect security, meaning that individuals who use these methods risk being detected. This is because previous steganography algorithms would subtly change the distribution of the innocuous content.
To overcome this, the research team used recent breakthroughs in information theory, specifically minimum entropy coupling, which allows one to join two distributions of data together such that their mutual information is maximised, but the individual distributions are preserved.
As a result, with the new algorithm, there is no statistical difference between the distribution of the innocuous content and the distribution of content that encodes sensitive information.
The algorithm was tested using several types of models that produce auto-generated content, such as GPT-2, an open-source language model, and WAVE-RNN, a text-to-speech converter. Besides being perfectly secure, the new algorithm showed up to 40% higher encoding efficiency than previous steganography methods across a variety of applications, enabling more information to be concealed within a given amount of data. This may make steganography an attractive method even if perfect security is not required, due to the benefits for data compression and storage.
The research team has filed a patent for the algorithm, but intend to issue it under a free licence to third parties for non-commercial responsible use. This includes academic and humanitarian use, and trusted third-party security audits. The researchers have published this work as a preprint paper, as well as open-sourced an inefficient implementation of their method on Github. They will also present the new algorithm at the premier AI conference, the 2023 International Conference on Learning Representations in May.

Co-lead author Dr Christian Schroeder de Witt (Department of Engineering Science, University of Oxford) said: ‘Our method can be applied to any software that automatically generates content, for instance probabilistic video filters, or meme generators. This could be very valuable, for instance, for journalists and aid workers in countries where the act of encryption is illegal. However, users still need to exercise precaution as any encryption technique may be vulnerable to side-channel attacks such as detecting a steganography app on the user’s phone.’
Contributing author Professor Jakob Foerster (Department of Engineering Science, University of Oxford) added: ‘This paper is a great example of research into the foundations of machine learning that leads to breakthrough discoveries for crucial application areas. It's wonderful to see that Oxford, and our young lab in particular, is at the forefront of it all.’
The paper ‘Perfectly Secure Steganography Using Minimum Entropy Coupling’ has been accepted for the 2023 International Conference on Learning Representations.
Besides Dr Christian Schroeder de Witt and Professor Jakob Foerster, the study involved Samuel Sokota and Professor Zico Kolter at Carnegie Mellon University, USA, and Dr Martin Strohmeier from armasuisse Science+Technology, Switzerland. The work was partially funded by a EPSRC IAA Doctoral Impact fund hosted by Professor Philip Torr, Torr Vision Group, at the University of Oxford.



